![]() In 4G, your IMSI was sent in plaintext. Any Stingray device could capture it.
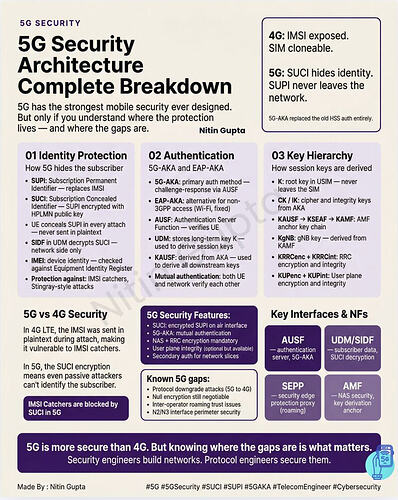
In 4G, your IMSI was sent in plaintext. Any Stingray device could capture it.
5G fixed this. But most engineers don’t know exactly how — or where the gaps still exist.
Here’s the complete 5G security breakdown:
![]() Identity Protection — How 5G Hides the Subscriber:
Identity Protection — How 5G Hides the Subscriber:
→ SUPI: Subscription Permanent Identifier — replaces the 4G IMSI
→ SUCI: Subscription Concealed Identifier — SUPI encrypted with HPLMN public key
→ UE encrypts SUPI before every attach — never sent in plaintext over the air
→ SIDF (in UDM) decrypts SUCI — only the home network can reveal the real identity
→ IMEI: device identity — checked against Equipment Identity Register (EIR)
→ Result: IMSI catchers and Stingray attacks are blocked at the identity level
![]() Authentication — 5G-AKA and EAP-AKA:
Authentication — 5G-AKA and EAP-AKA:
→ 5G-AKA: primary authentication — challenge-response via AUSF and UDM
→ EAP-AKA: used for non-3GPP access (Wi-Fi calling, fixed wireless)
→ AUSF: Authentication Server Function — verifies the UE identity
→ UDM: stores the long-term key K — used to derive all session keys
→ KAUSF → KSEAF → KAMF: key chain from auth to AMF anchor
→ Mutual authentication: both UE AND the network verify each other — 4G only authenticated the UE
![]() The 5G Key Hierarchy:
The 5G Key Hierarchy:
→ K: root key stored in USIM — never leaves the SIM
→ CK / IK: cipher and integrity keys derived from AKA
→ KgNB: derived from KAMF — the gNB session key
→ KRRCenc + KRRCint: RRC layer encryption and integrity
→ KUPenc + KUPint: user plane encryption and integrity (integrity optional but available)
![]() Where 5G security gaps still exist:
Where 5G security gaps still exist:
× Protocol downgrade attacks: UE can be forced to 4G where SUCI doesn’t apply
× Null encryption: still negotiable in some operator configurations — should not be
× Inter-operator roaming: N32 interface between SEPPs relies on operator trust
× User plane integrity: optional by 3GPP — not all operators enable it
× False base station attacks: still possible in some NSA deployments
![]() Key Security NFs every engineer must know:
Key Security NFs every engineer must know:
→ AUSF — authenticates UE, issues KAUSF
→ UDM/SIDF — stores subscriber key K, decrypts SUCI
→ SEPP — Security Edge Protection Proxy — secures N32 roaming interface
→ AMF — NAS security context holder, derives KgNB for gNB
5G is the most secure mobile generation ever designed. But security only holds if operators enable all features — and engineers understand where the boundaries are.
LinkedIn: ![]()