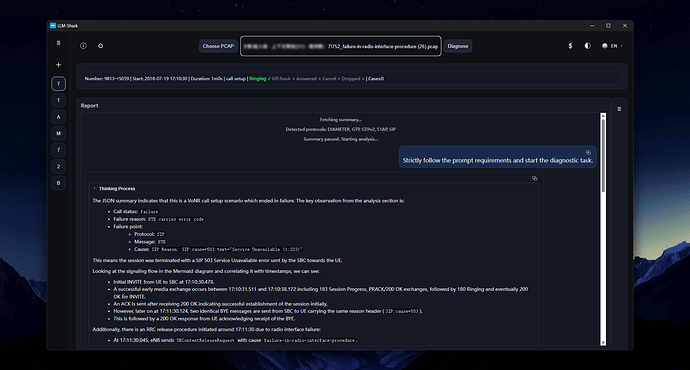
LLM-Shark is a conversational PCAP signaling analysis tool capable of diagnosing complex VoNR/VoLTE call failures.
An engineer friend asked: “How can I use this tool to analyze LTE signaling?”
My response was: “Just tell it directly.”
Because when you’re using llm-shark, you’re essentially having a conversation with AI. You need to truly realize that the LlmShark on the other side is an AI capable of dialogue!
Below is an example using a signaling packet (PCAP) to demonstrate the effect.
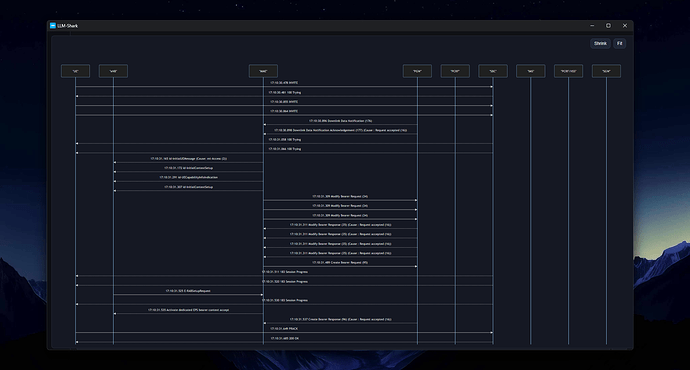
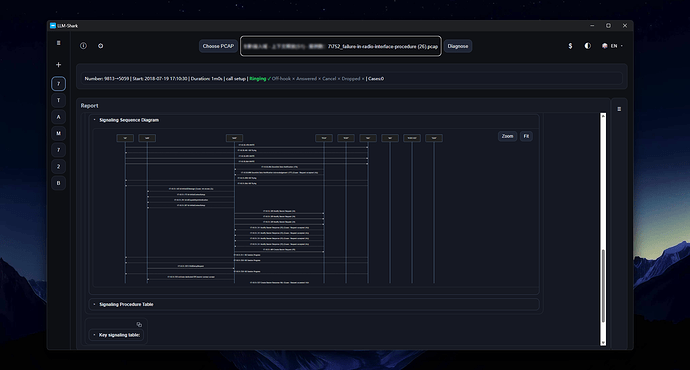
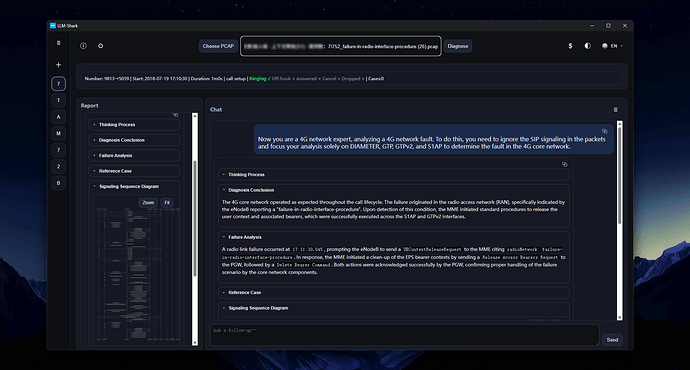
During normal diagnostic execution, llm-shark comprehensively analyzes all these protocol signals—DIAMETER, GTP, GTPv2, S1AP, and SIP—before providing diagnostic conclusions. The signaling sequence diagrams it generates also show the complete call process.
If you only want to analyze 4G signaling, simply say so directly in the chat window—ask it to analyze only 4G network faults.
Now you are a 4G network expert, analyzing a 4G network fault. To do this, you need to ignore SIP signaling in the packets and focus your analysis solely on DIAMETER, GTP, GTPv2, and S1AP to determine faults in the 4G core network.
llm-shark transforms into a 4G core network expert and re-analyzes, providing diagnostic conclusions. For example, in this case, its conclusion was that there was no problem with the core network—the fault appeared in the access network.
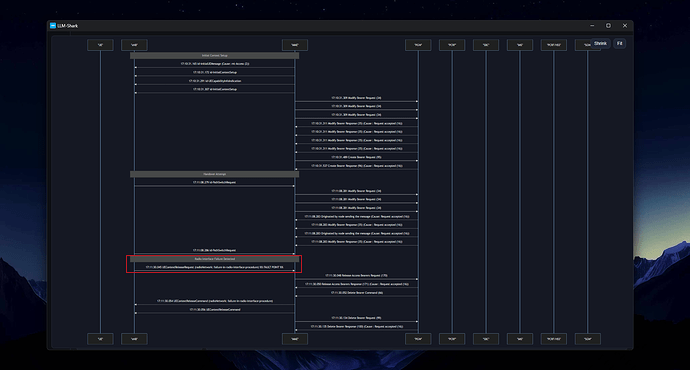
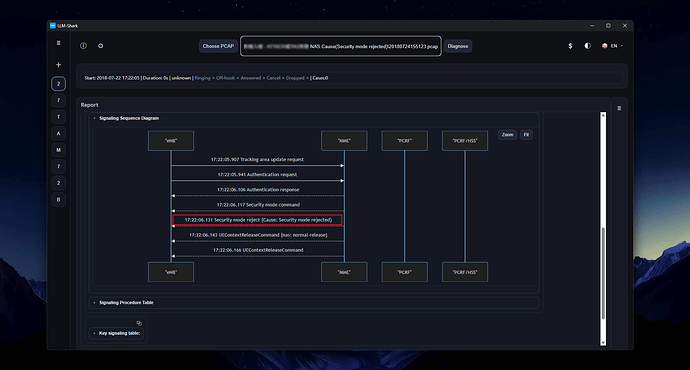
Switching to another signaling packet with pure 4G protocols and no SIP signaling.
Since there is no SIP content in this signaling packet, it directly proceeds with 4G core network fault localization analysis.
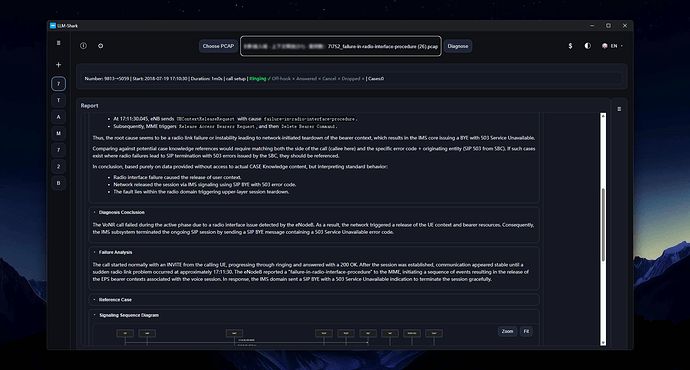
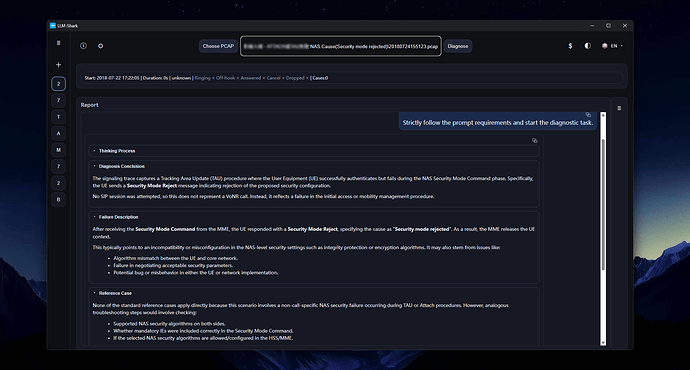
Diagnostic Conclusion
This signaling flow is a Tracking Area Update (TAU) procedure that failed because the UE rejected network commands during the security mode establishment phase—not a VoNR/VoLTE call flow. The direct cause of failure was the UE replying with a Security Mode Reject, carrying NAS cause value #14 (Security mode rejected).
Fault Process Analysis
- Flow Starting Point: The UE initiates a Tracking Area Update request to the MME via the eNB.
- Network Authentication: The MME initiates the authentication procedure, which completed successfully.
- Security Activation Failure: The MME issues a Security Mode Command, requiring activation of integrity protection and encryption for signaling. The UE replies with Security Mode Reject, with cause value “Security mode rejected.” This indicates the UE cannot accept the security algorithms provided by the network or there is a security context issue.
- Connection Release: Subsequently, the MME initiates a UE Context Release command, releasing the S1 connection for this UE.
Root Cause Speculation: There is a mismatch in security capabilities (such as encryption/integrity protection algorithms) between the UE and the MME in the network core, or there is an anomaly with the UE’s USIM card, causing it to be unable to comply with the network’s security mode commands.
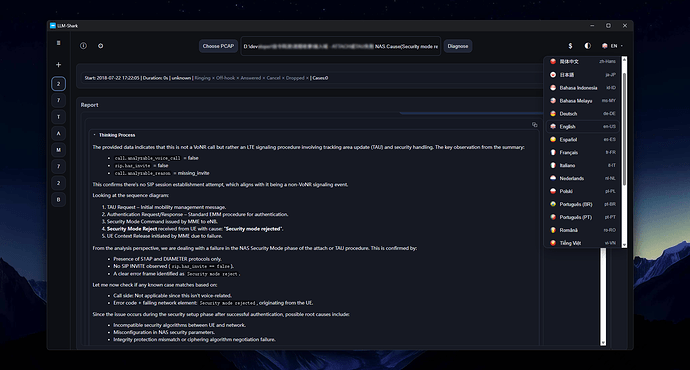
The signaling process is simple, and when you open the signaling sequence diagram, there are only a few network elements.
You can download llm-shark at the below link:
Looking forward to more feedback from everyone!